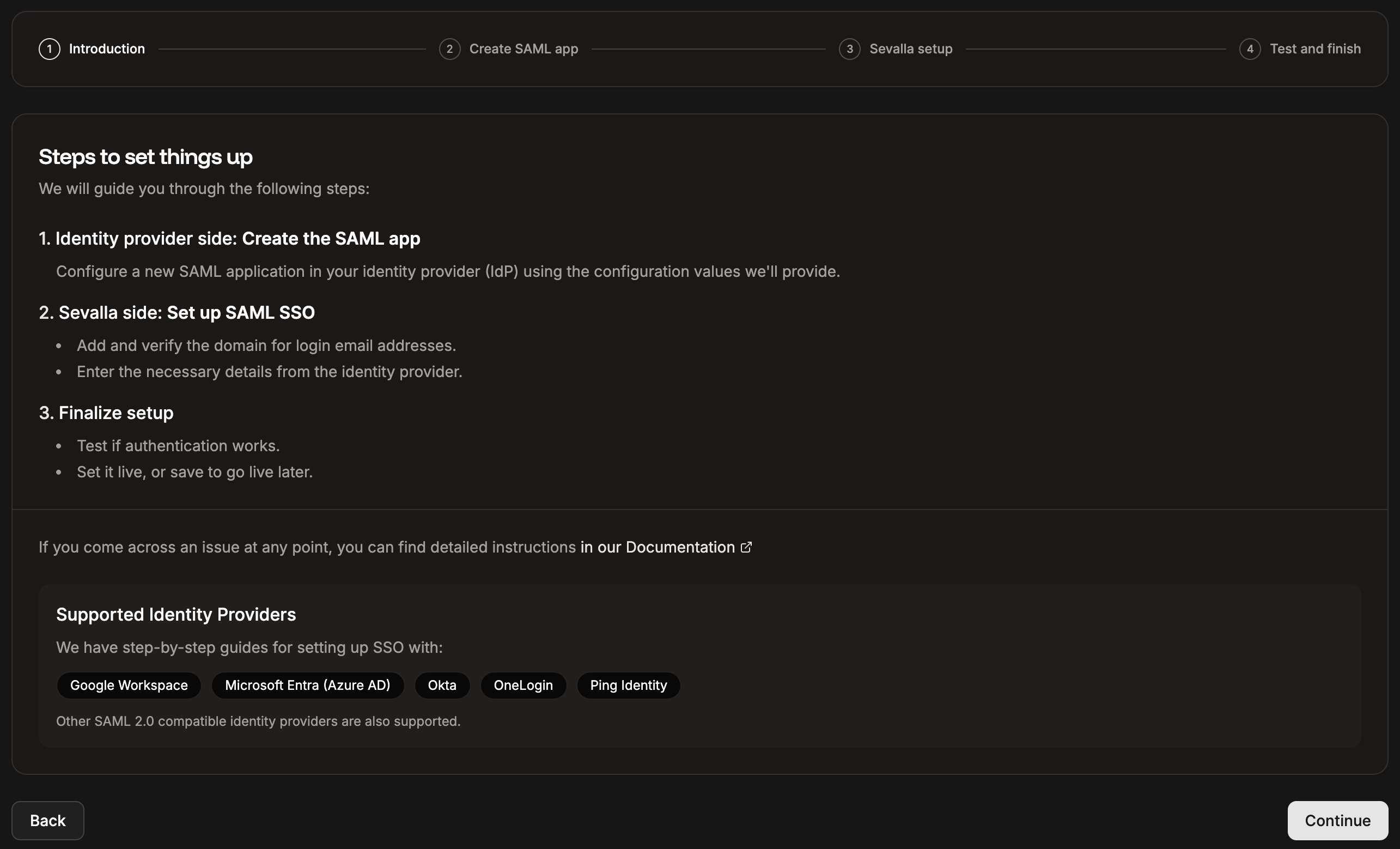
Okta is an Identity Provider (IdP) that enables secure single sign-on (SSO), allowing your company’s users to access multiple applications with one login. With Security Assertion Markup Language (SAML) SSO, employees sign in once using their company credentials (typically email and password). The IdP, such as Okta, verifies their identity and grants seamless, secure access to all connected services, without requiring separate logins for each application. Company owners or IT administrators can link their organization’s email domain (e.g., @mycompany.com) to the IdP so that anyone with a company email address is automatically recognized and can securely sign in to SAML-enabled tools. Using Sevalla SAML SSO, you can connect Okta to Sevalla by creating a SAML application within Okta, verifying your company’s email domain, and adding the required Okta details in Sevalla. This allows your team to log in with their existing company credentials, eliminating the need to create or manage separate Sevalla accounts.Documentation Index
Fetch the complete documentation index at: https://docs.sevalla.com/llms.txt
Use this file to discover all available pages before exploring further.
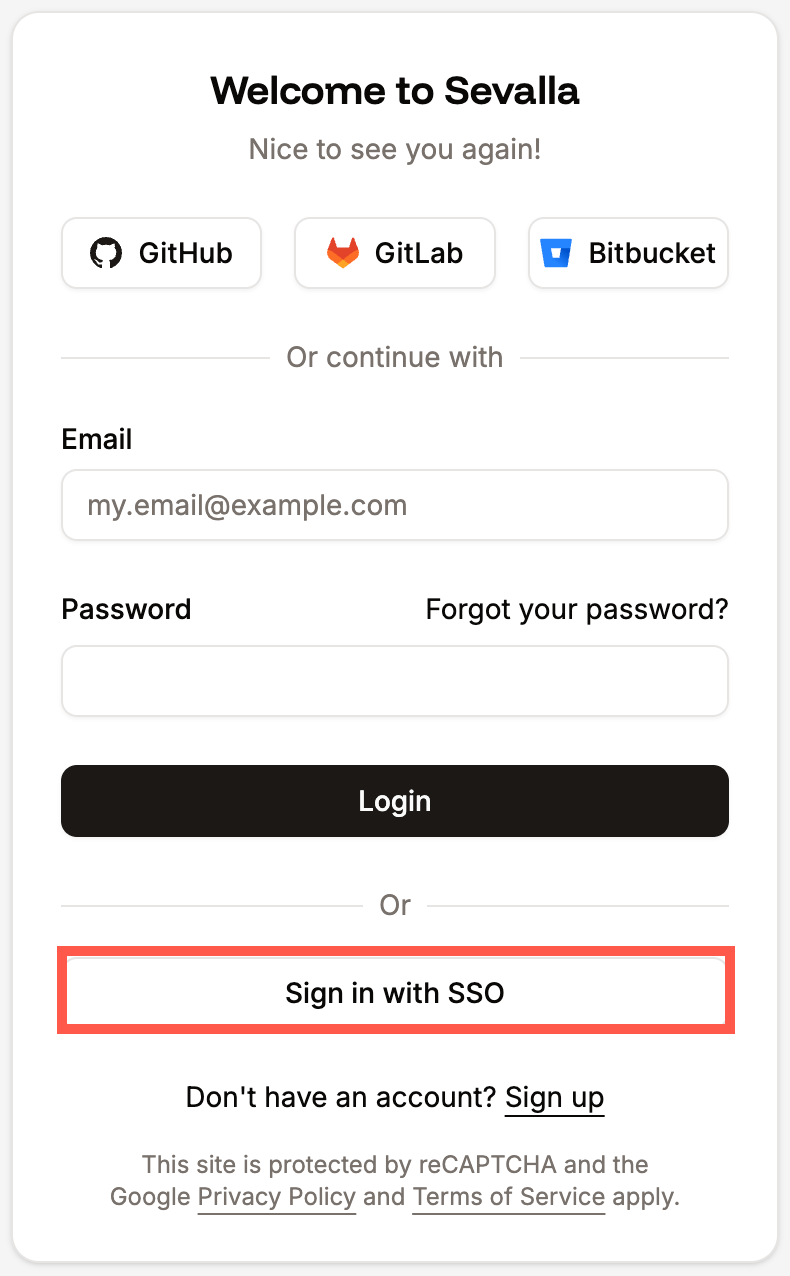
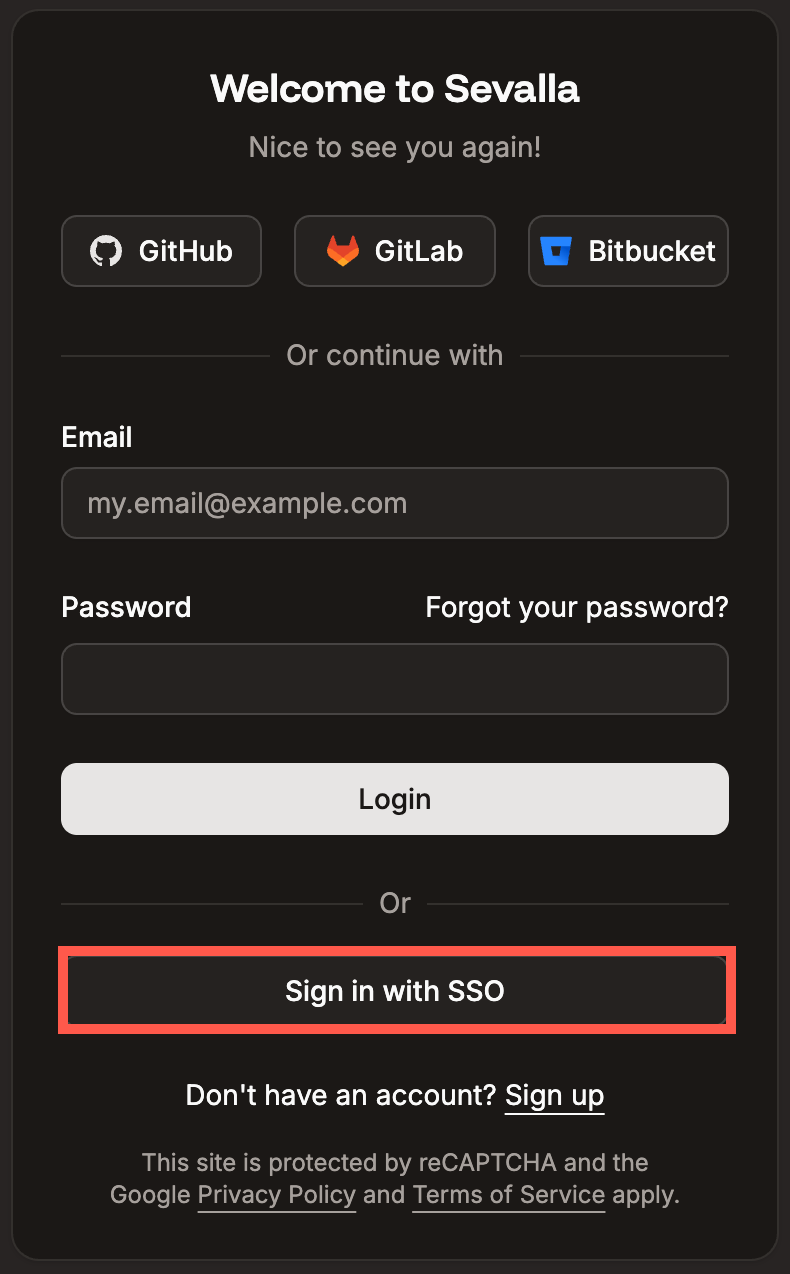
When using SAML SSO with Sevalla, login must always be initiated from Sevalla. Logging in directly from your Identity Provider (IdP) is not supported.IdPs only support one active session per browser. If you have multiple Google Workspace accounts and are logged into one, attempting to log into another through Sevalla will result in an error. To switch accounts, log out of Google Workspace or use your browser’s Incognito/Private mode.
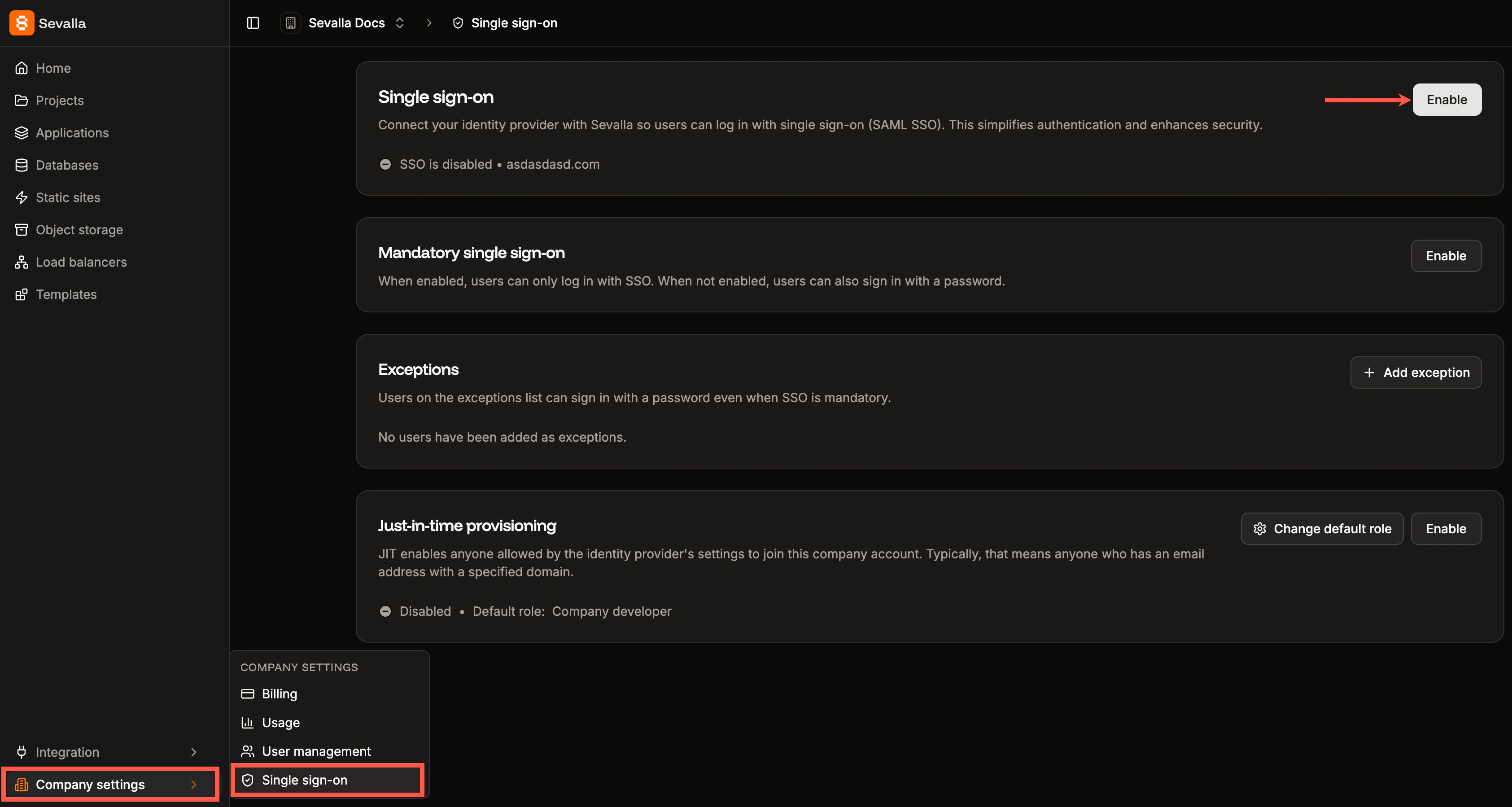
Enable SSO in Sevalla
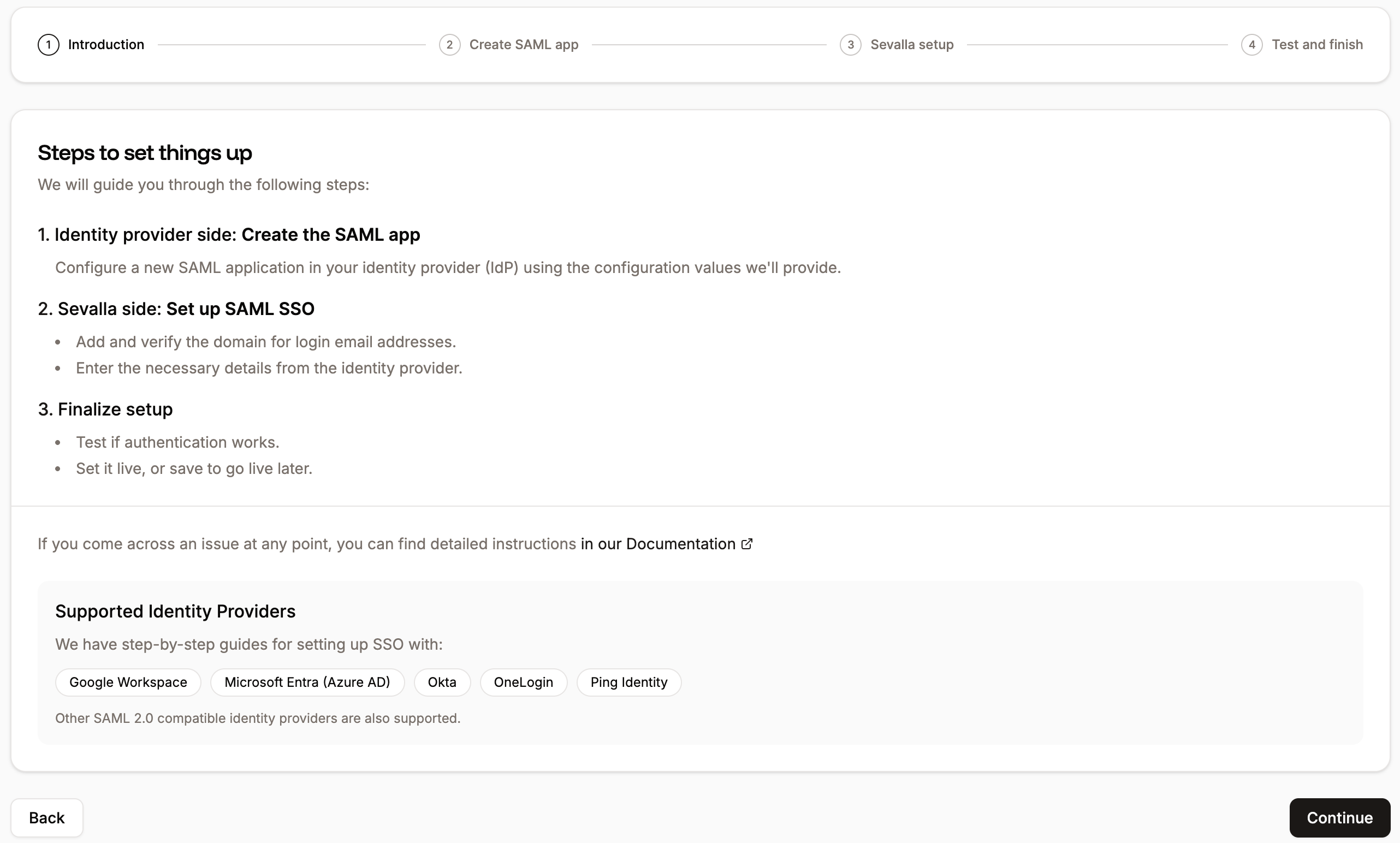
When you set up SAML SSO, you can navigate away from the SSO setup at any stage to store your progress and return later. In Sevalla, go to your Company settings > Single sign-on, and click Enable.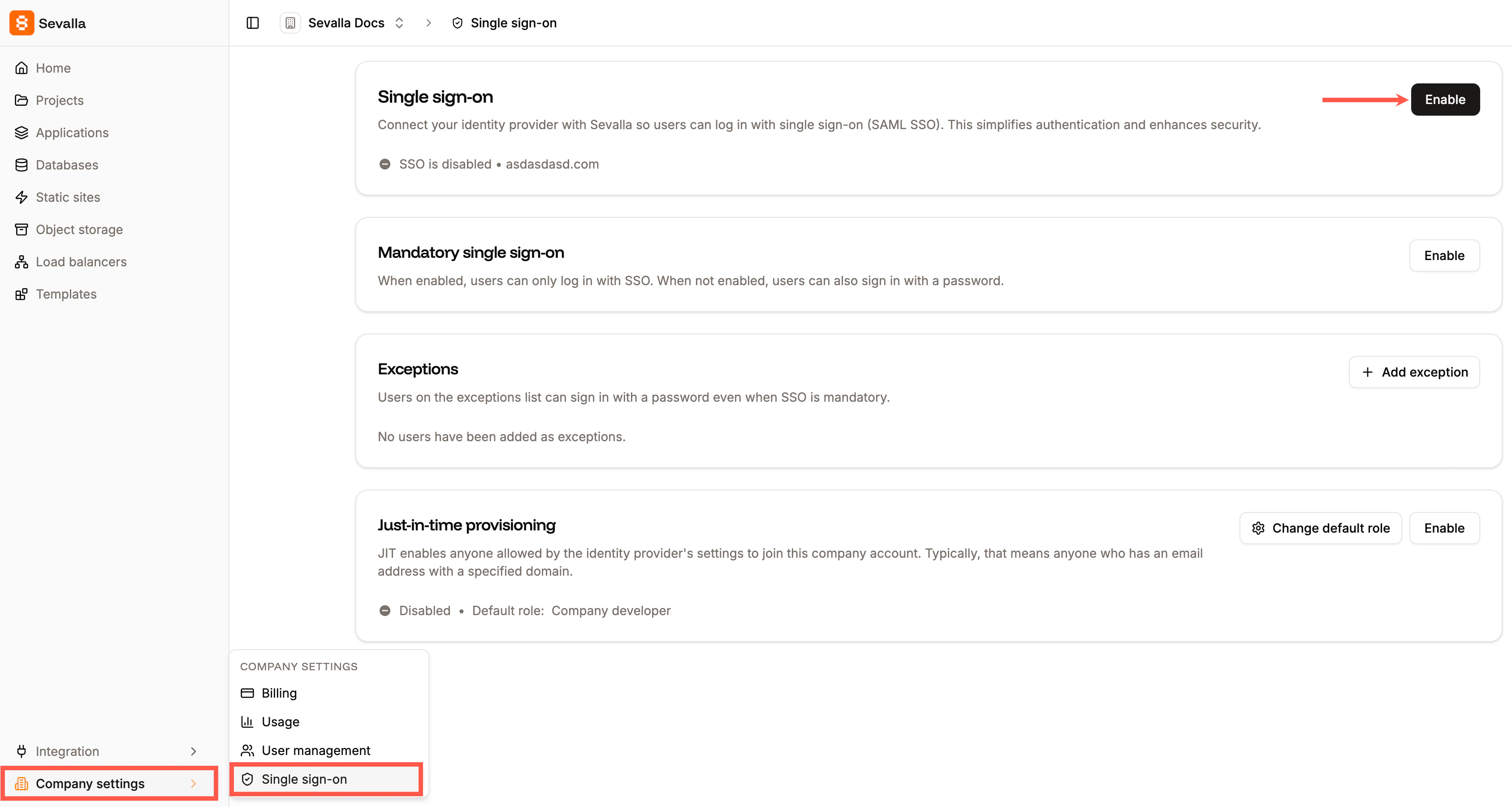
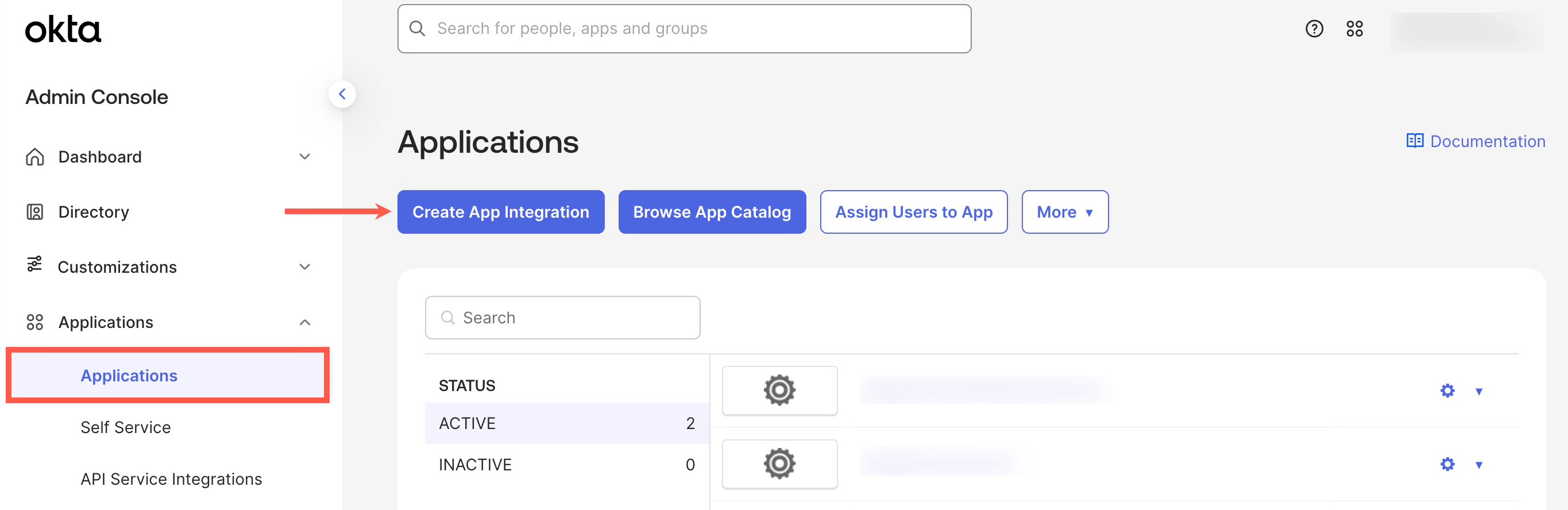
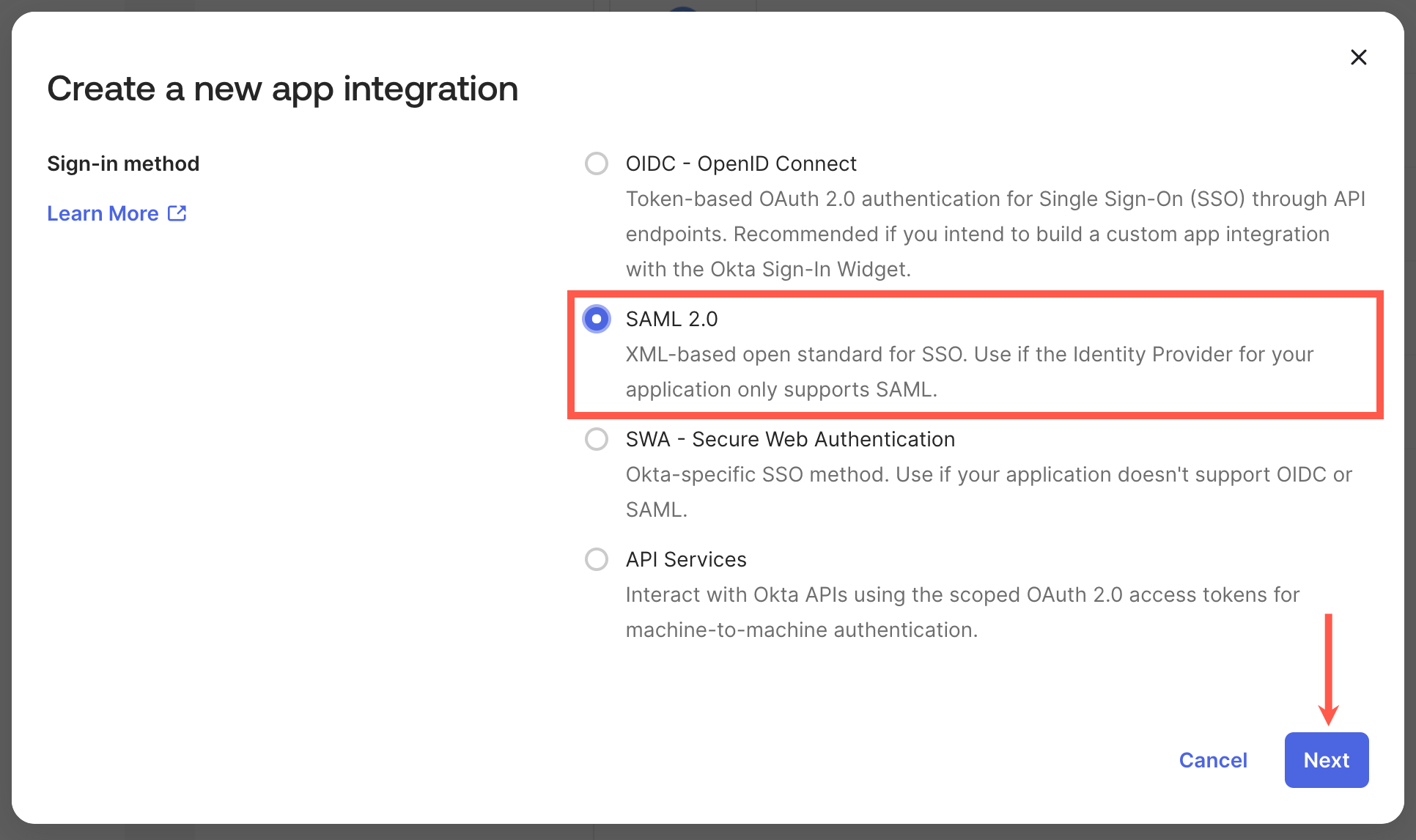
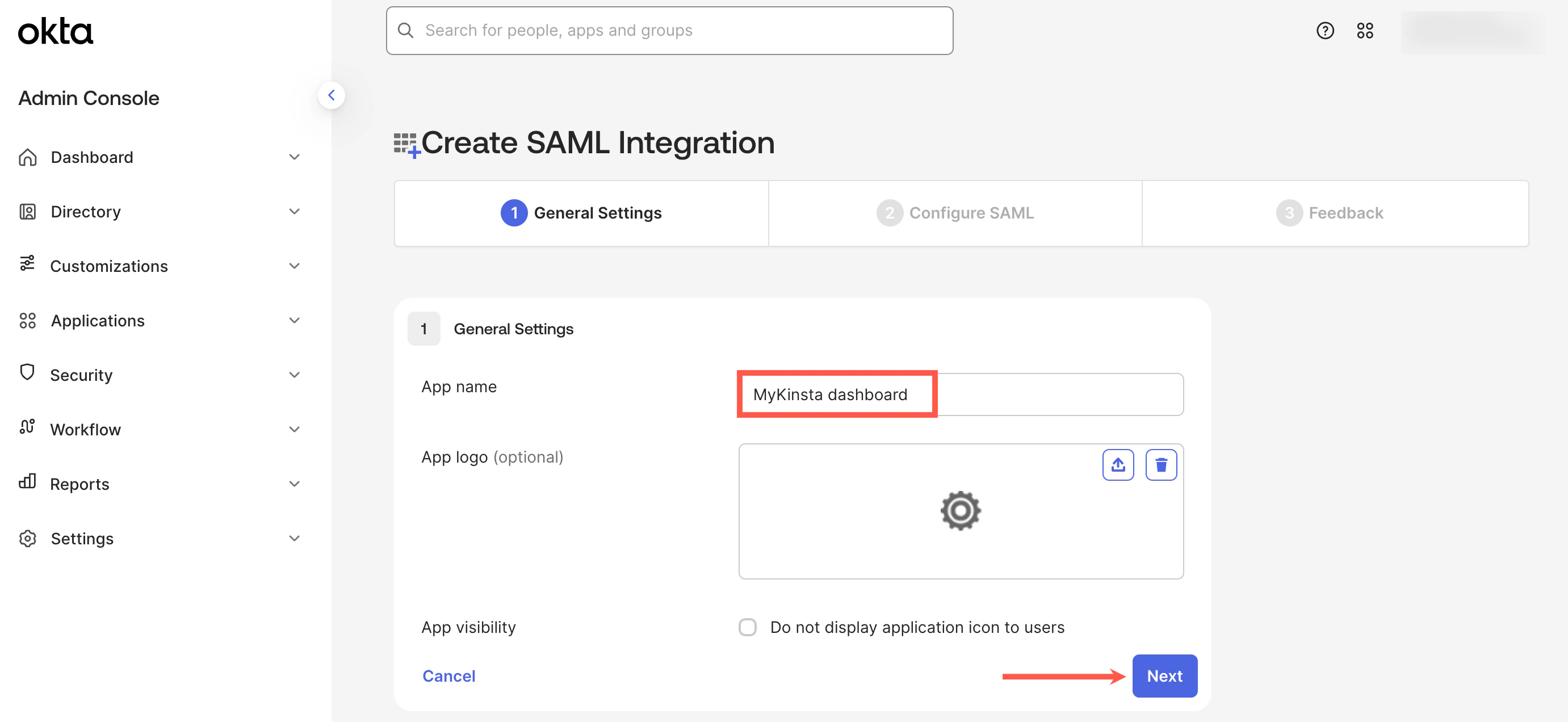
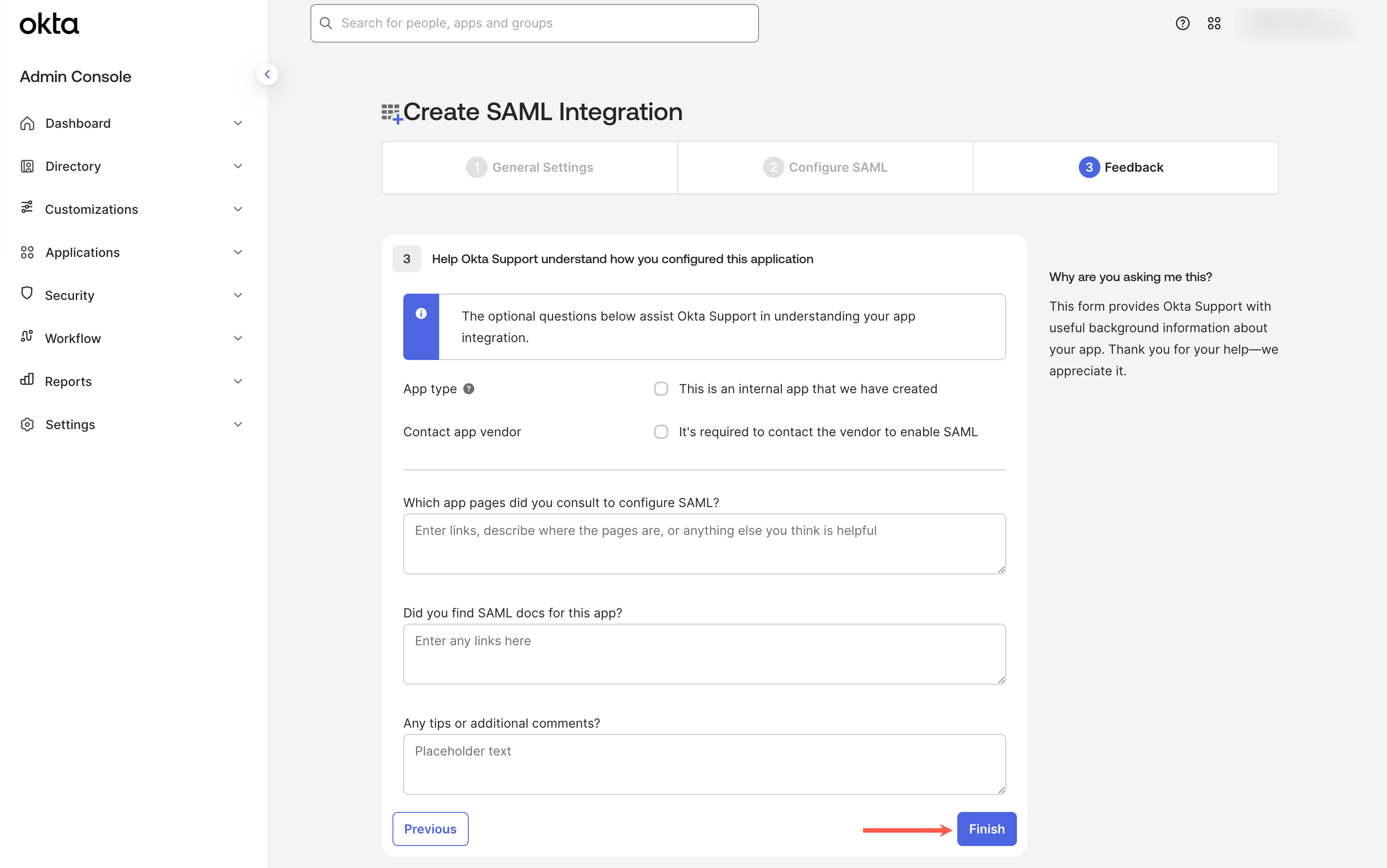
Set up the app integration in Okta
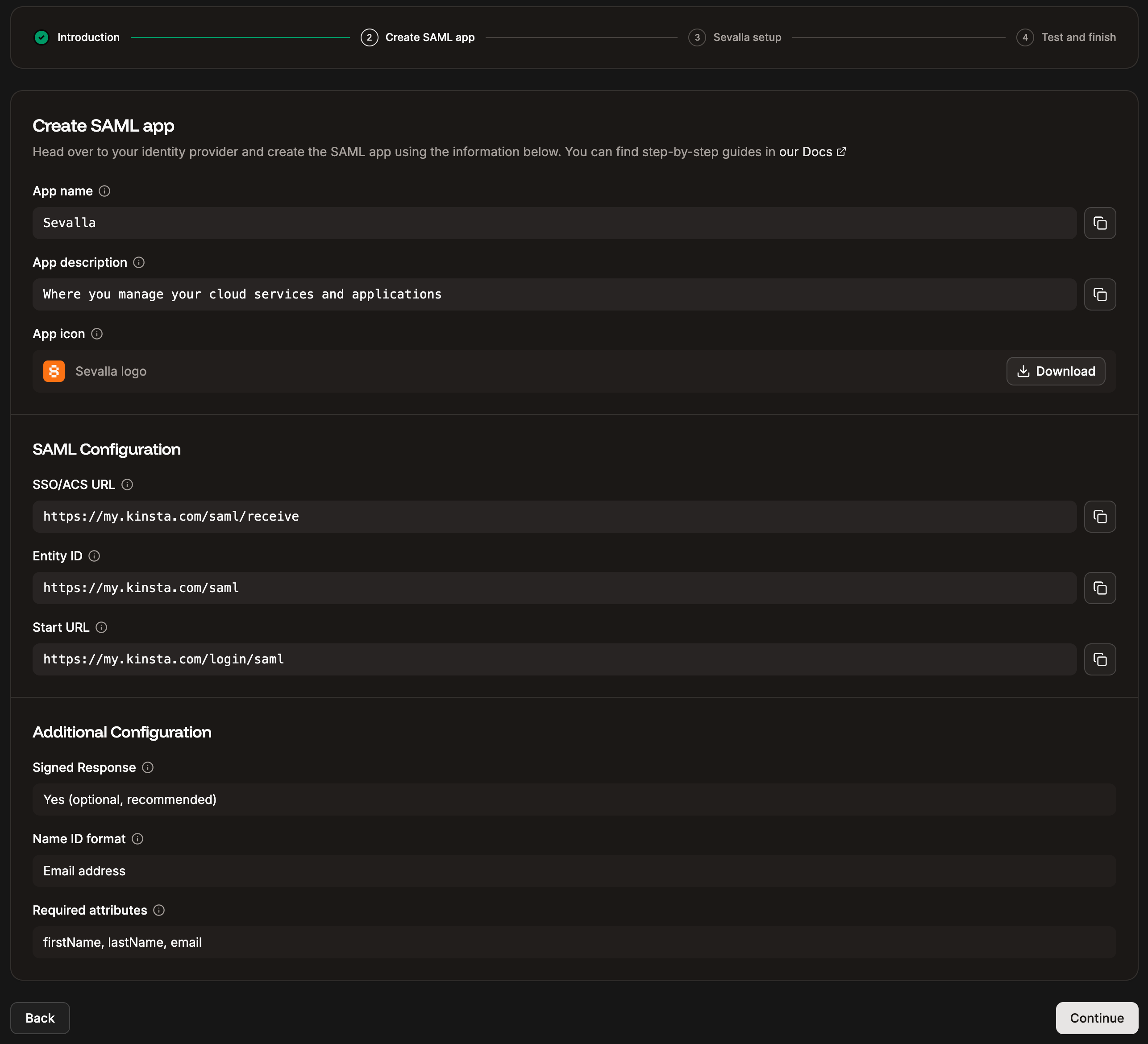
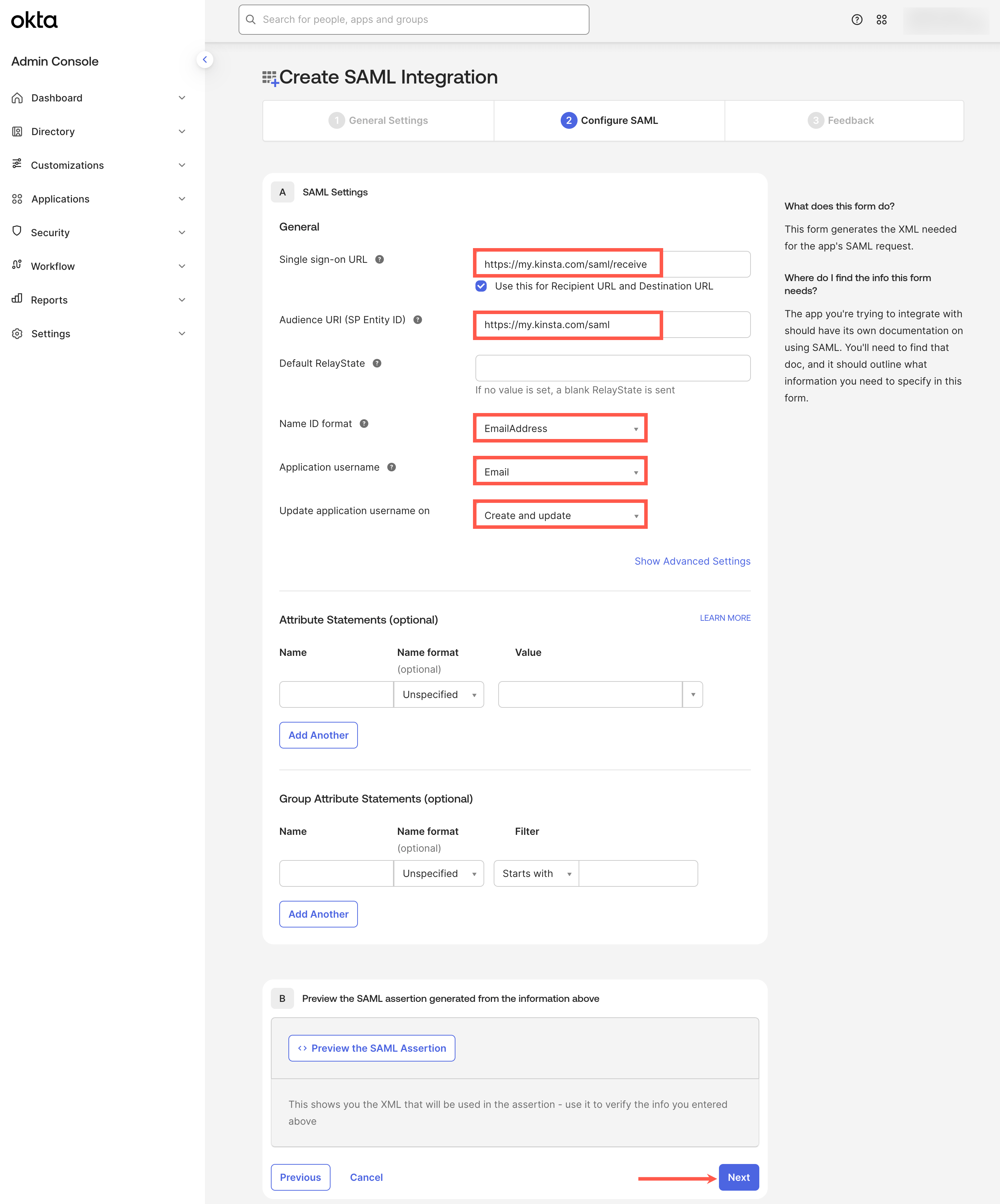
In Sevalla, the Create SAML app tab provides all the information you need to set up your SAML app within Okta. The following steps explain where to add this information.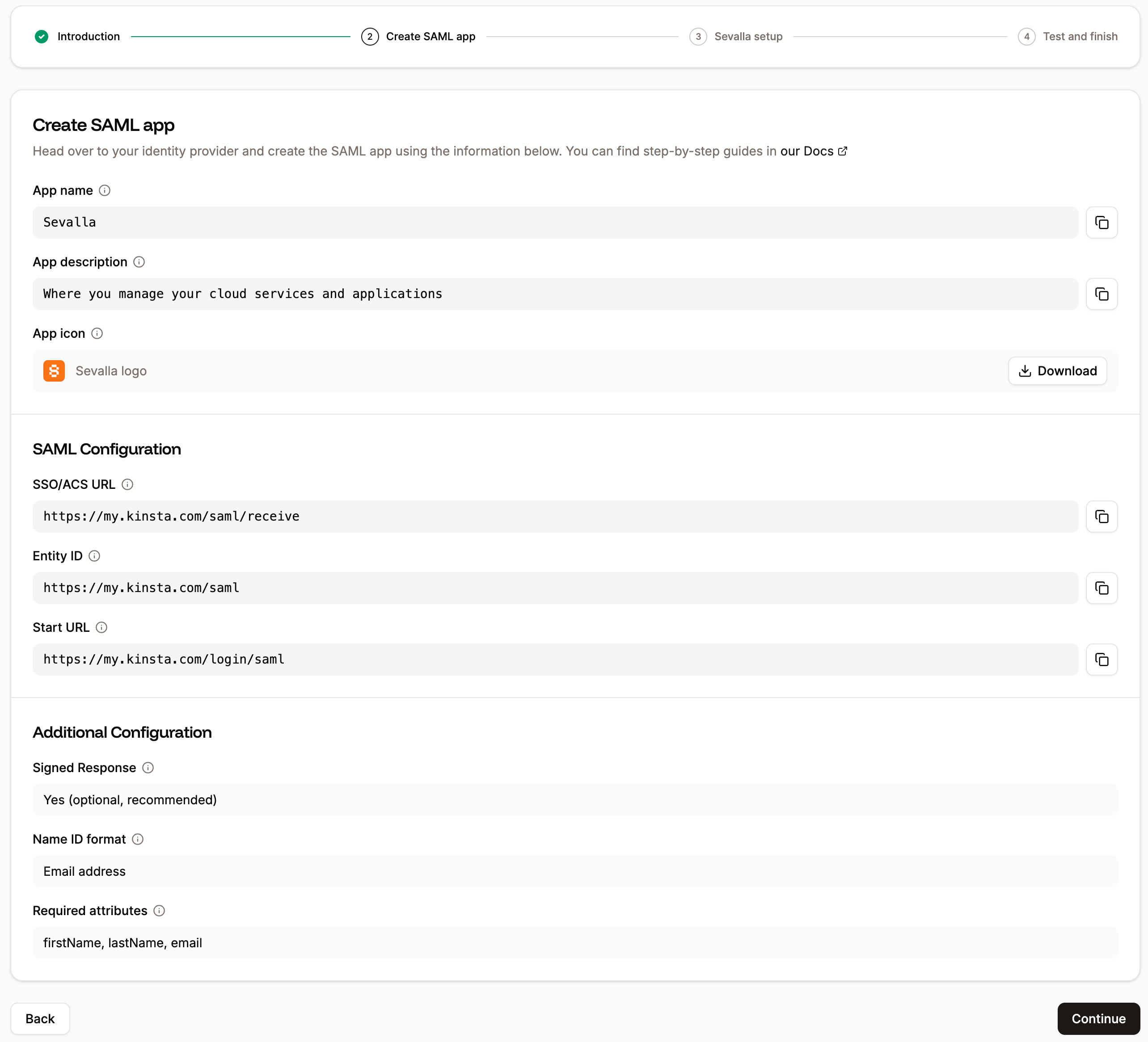
- Single sign-on URL: Copy and paste the SSO/ACS URL from Sevalla.
- Audience URI (SP Entity ID): Copy and paste the Entity ID from Sevalla.
- Name ID format: EmailAddress
- Application username: Email
- Update application username on: Create and update
Map your Okta attributes
Within Okta, you must map the firstName, lastName, and email attributes from Sevalla to the correct fields within Okta. For more information about how to do this, refer to the Okta docs.Assign users to the Okta app
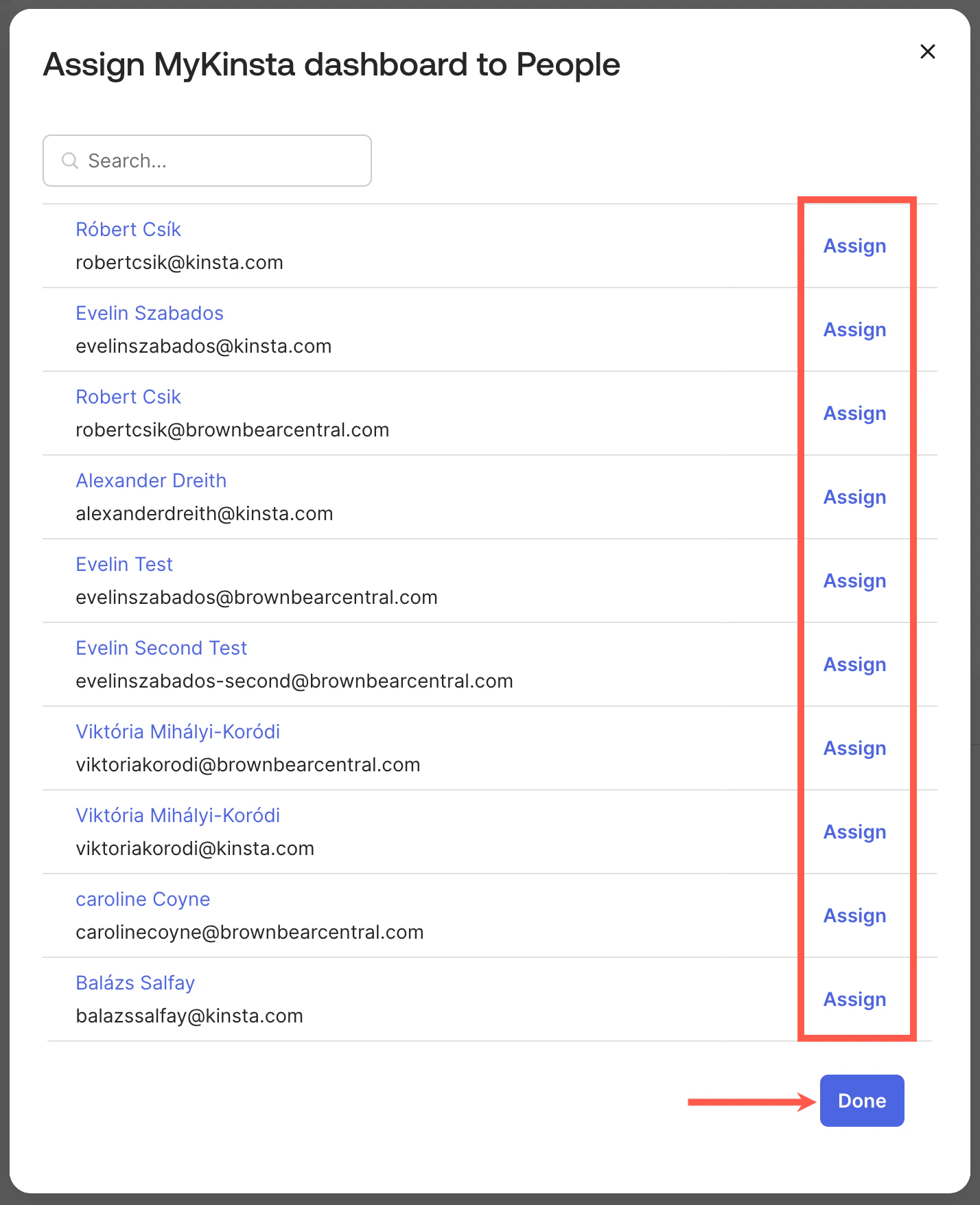
In Okta, go to Applications, select the application you set up for the Sevalla Dashboard, and click Assignments.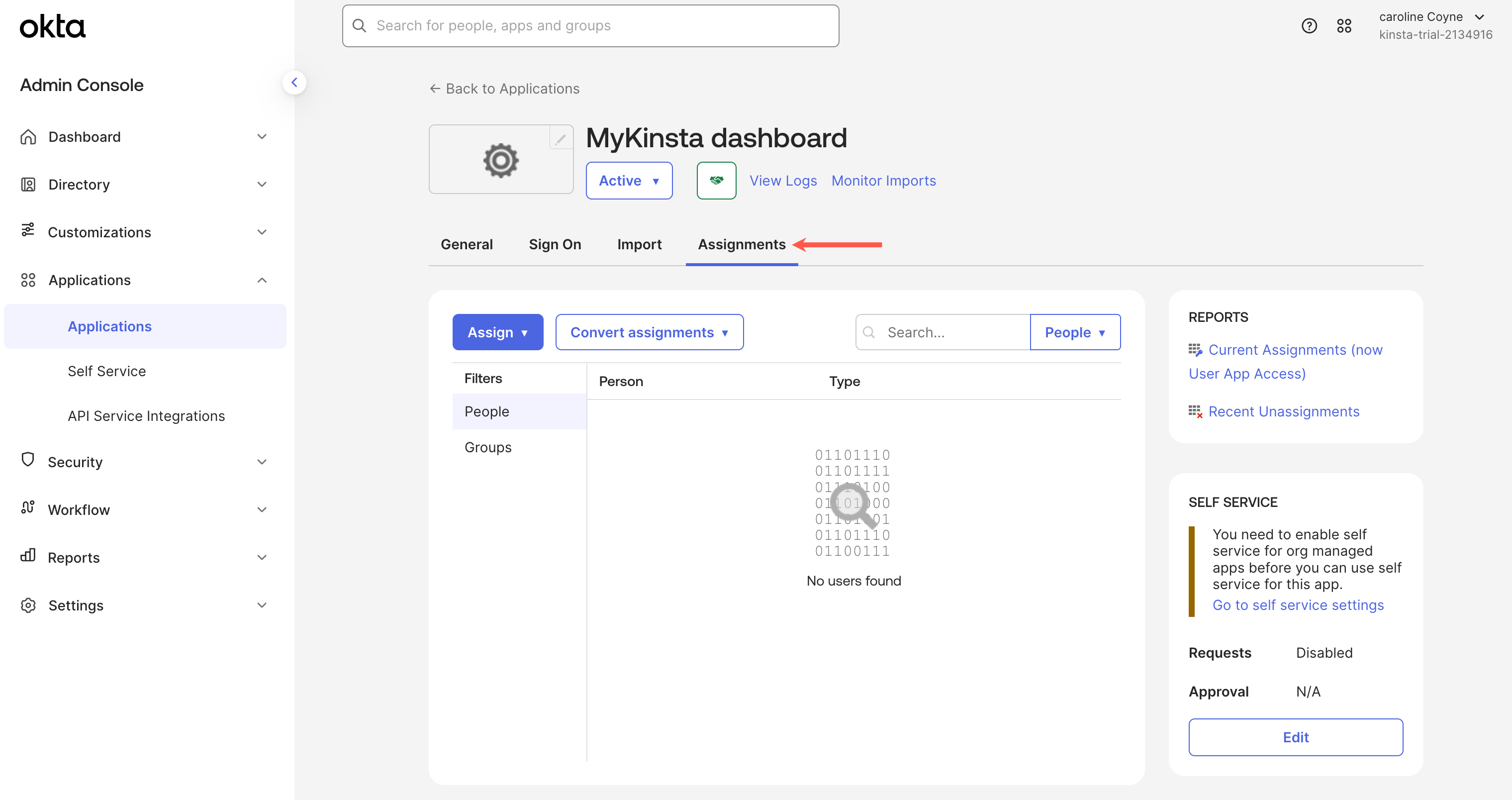
Sevalla setup
In Sevalla, on Create SAML app, click Continue so that you are on the Sevalla setup page.Email domain
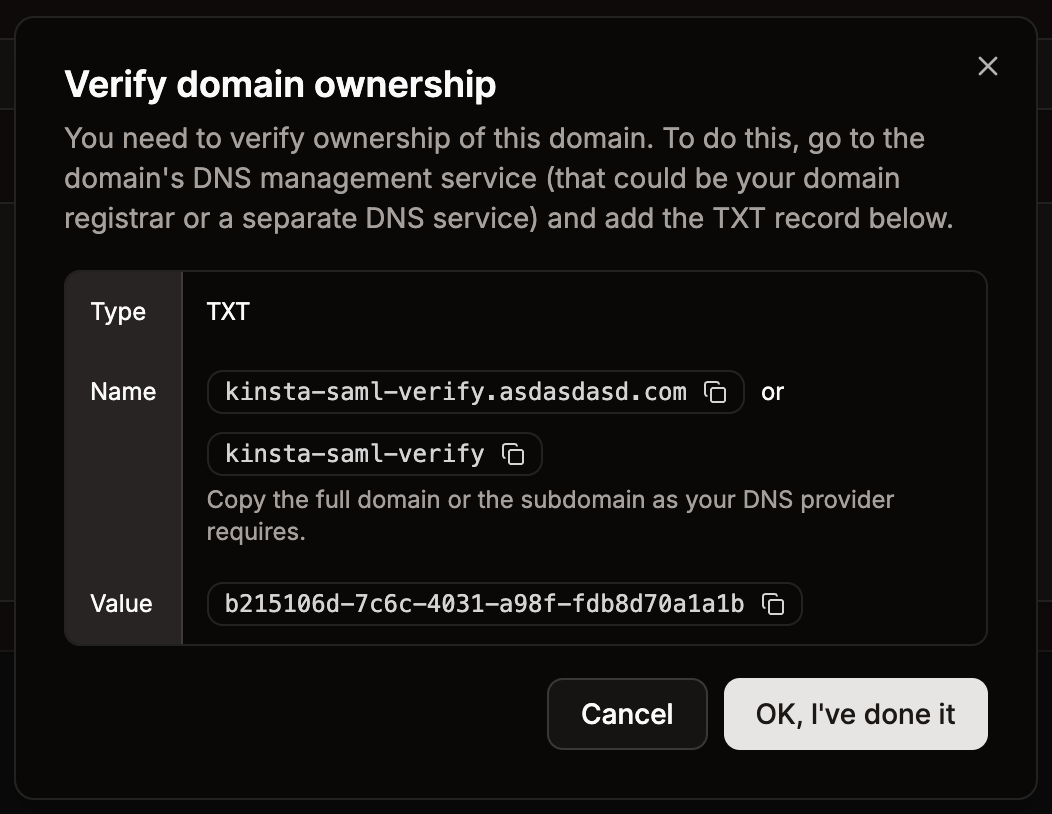
In the Domain name, enter the email domain users will use to sign in using SAML SSO, and click Add domain. Only Sevalla accounts with an email address matching the verified domain can authenticate via SAML. For example, if SAML is enabled forexample.com, only users with an @example.com email address will be able to sign in for that company.
Each email address can only be linked to one SAML configuration in Sevalla. This means a domain (e.g.,
example.com) can be associated with only one company at a time. Similarly, each Sevalla user can use SAML authentication for a single company only.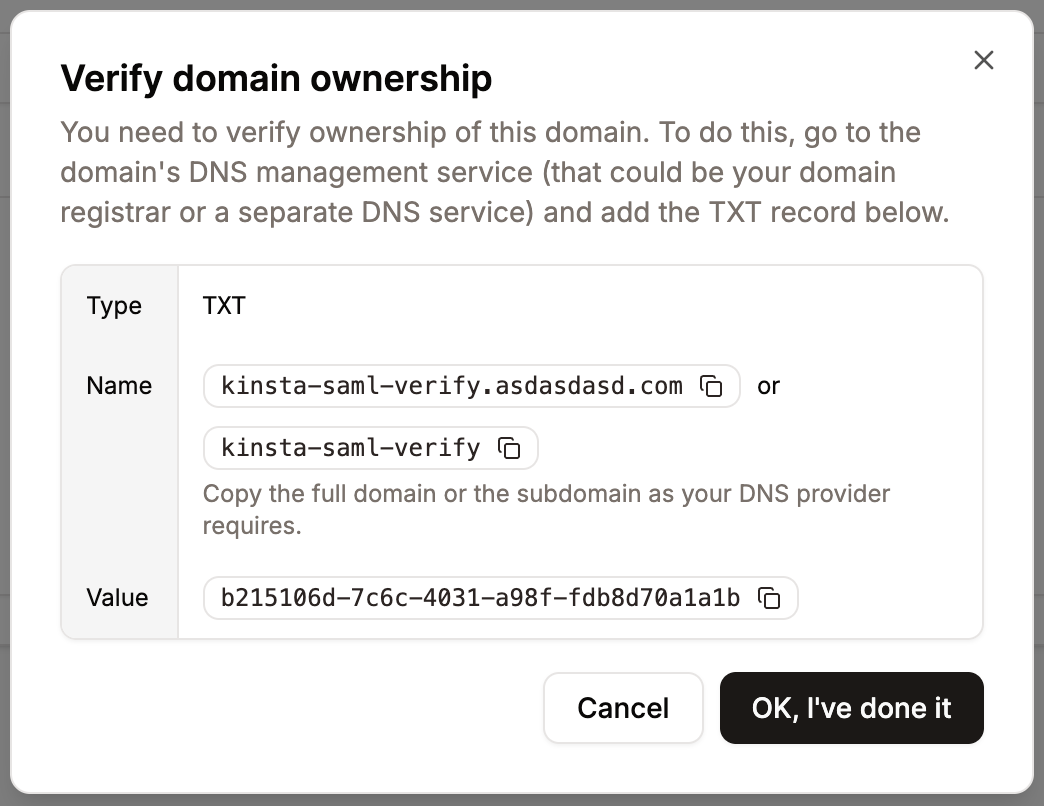
Set up Sevalla SAML
In Okta, go to Applications, select the application you set up for the Sevalla Dashboard, click Sign On, and then clickView SAML setup instructions .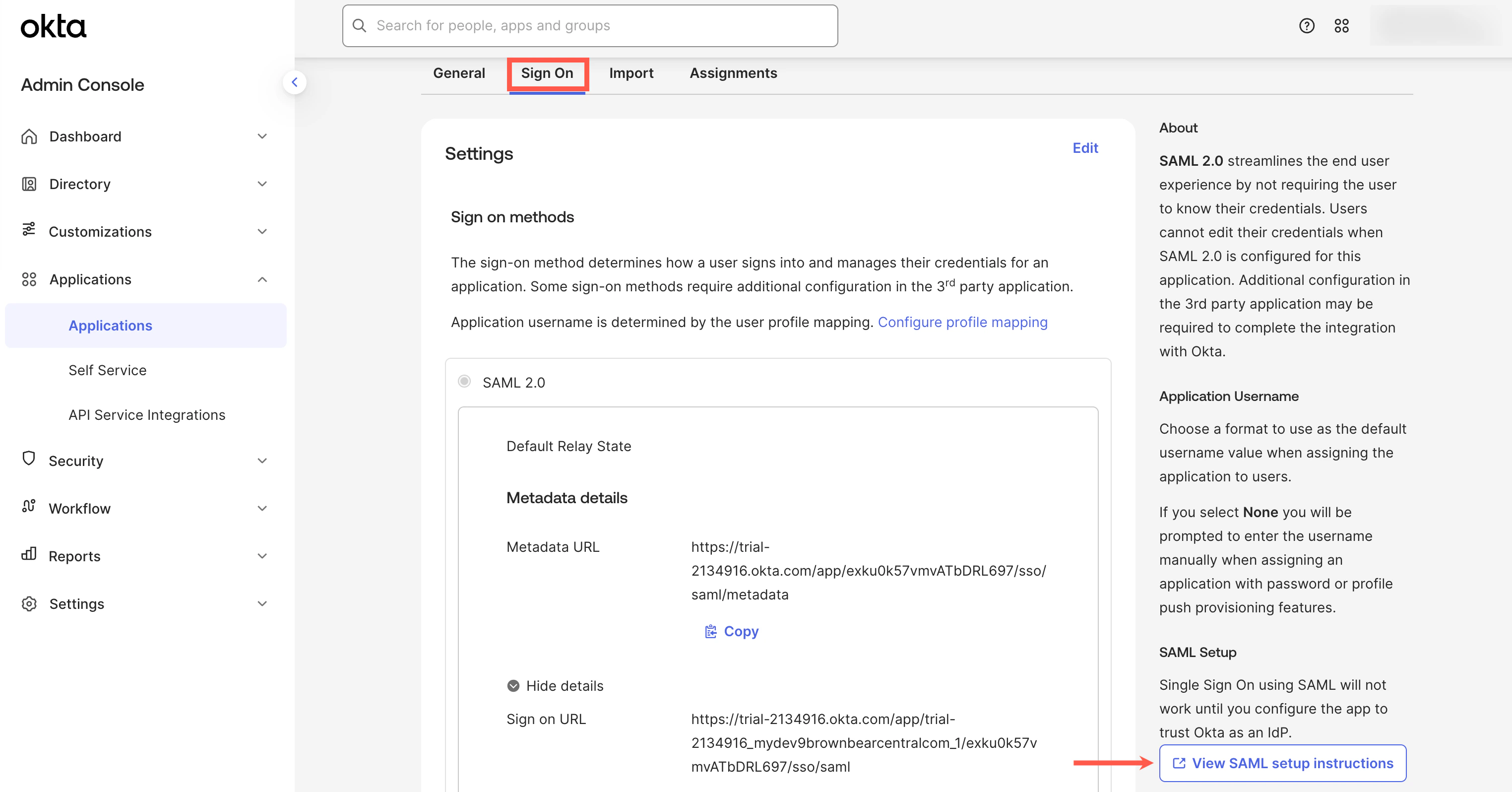
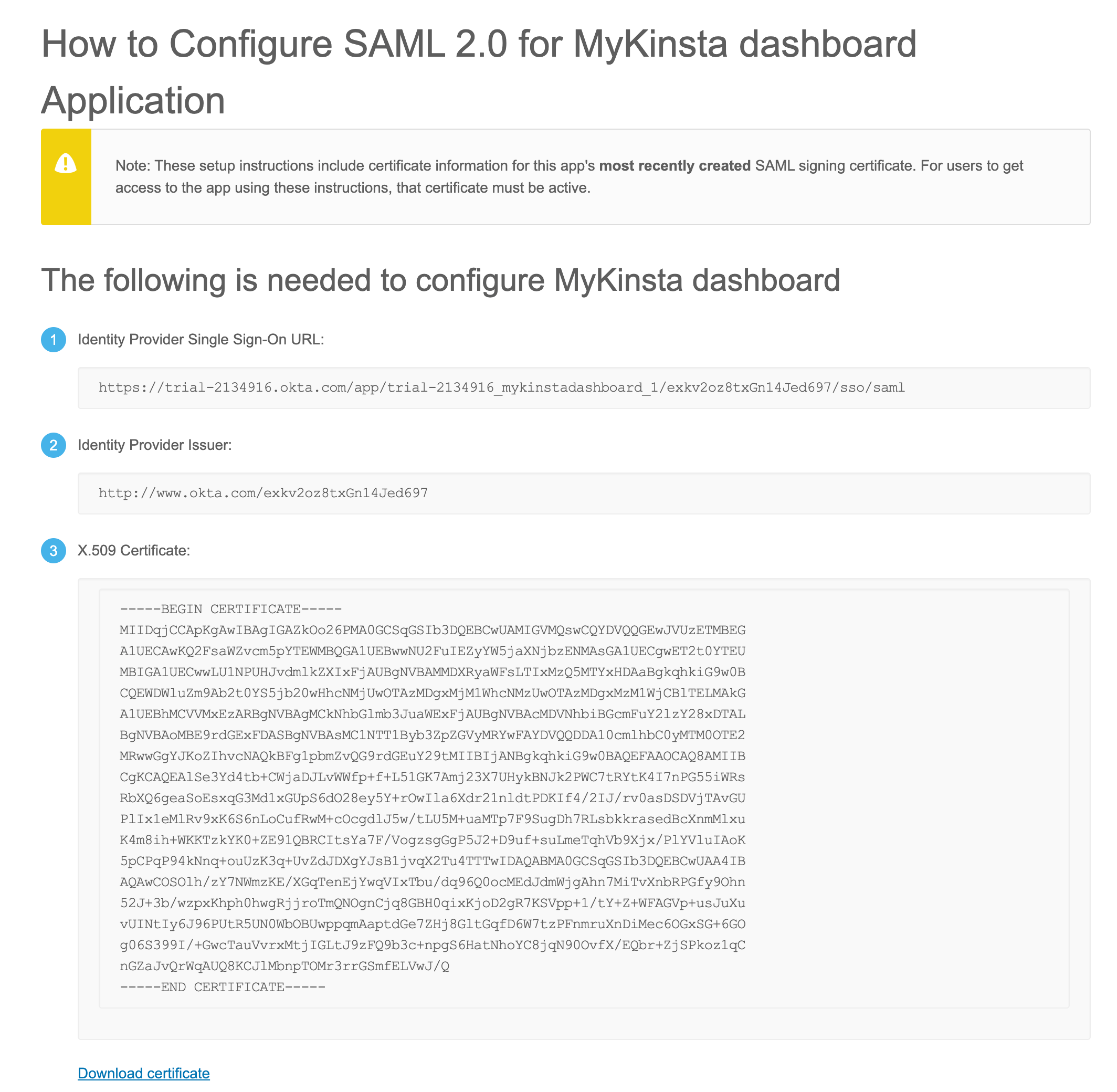
- SSO URL: Copy and paste the Identity Provider Single Sign-On URL from Okta.
- Entity ID: Copy and paste the Identity Provider Issuer from Okta.
- Public certificate: Copy and paste the X.509 Certificate from Okta.
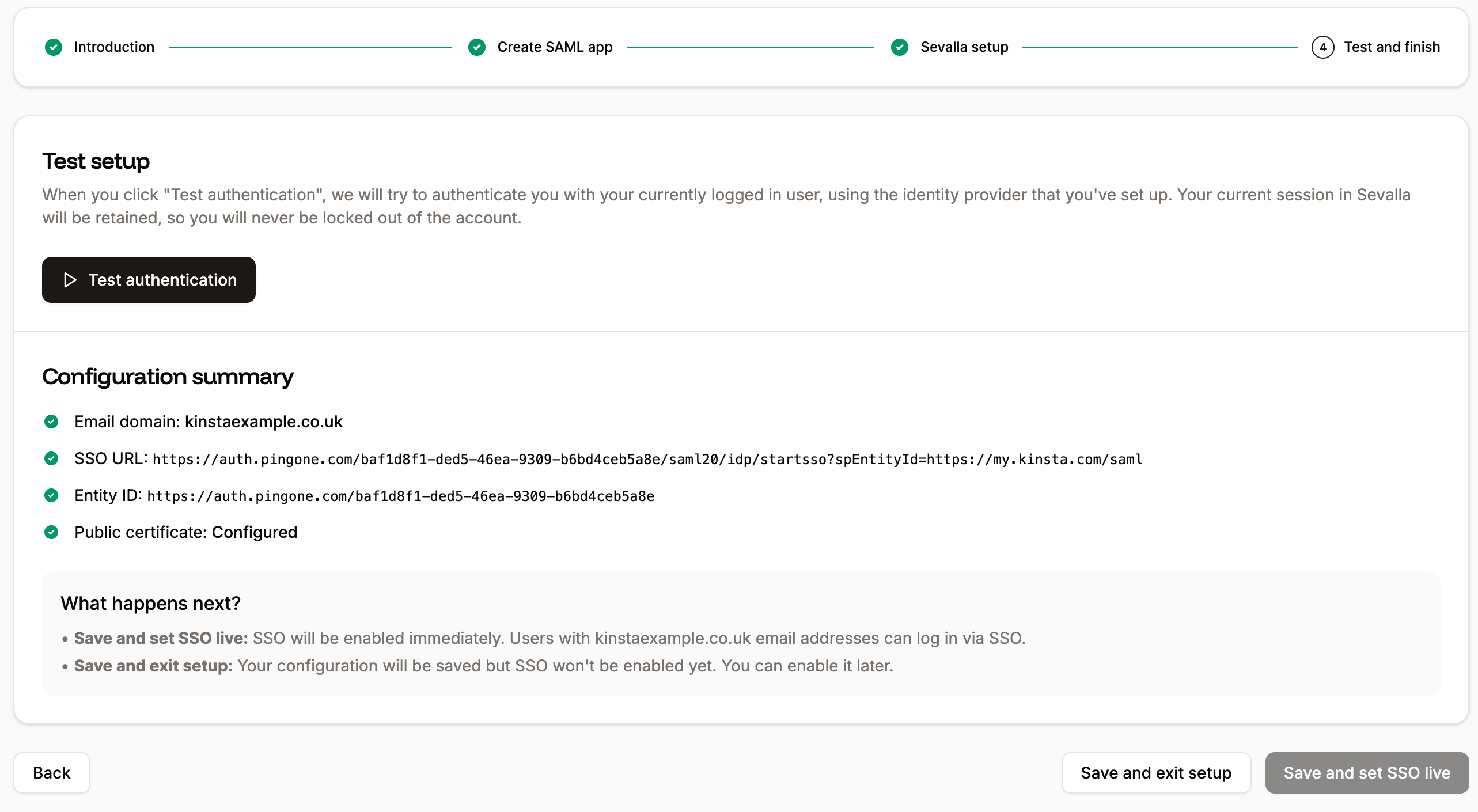
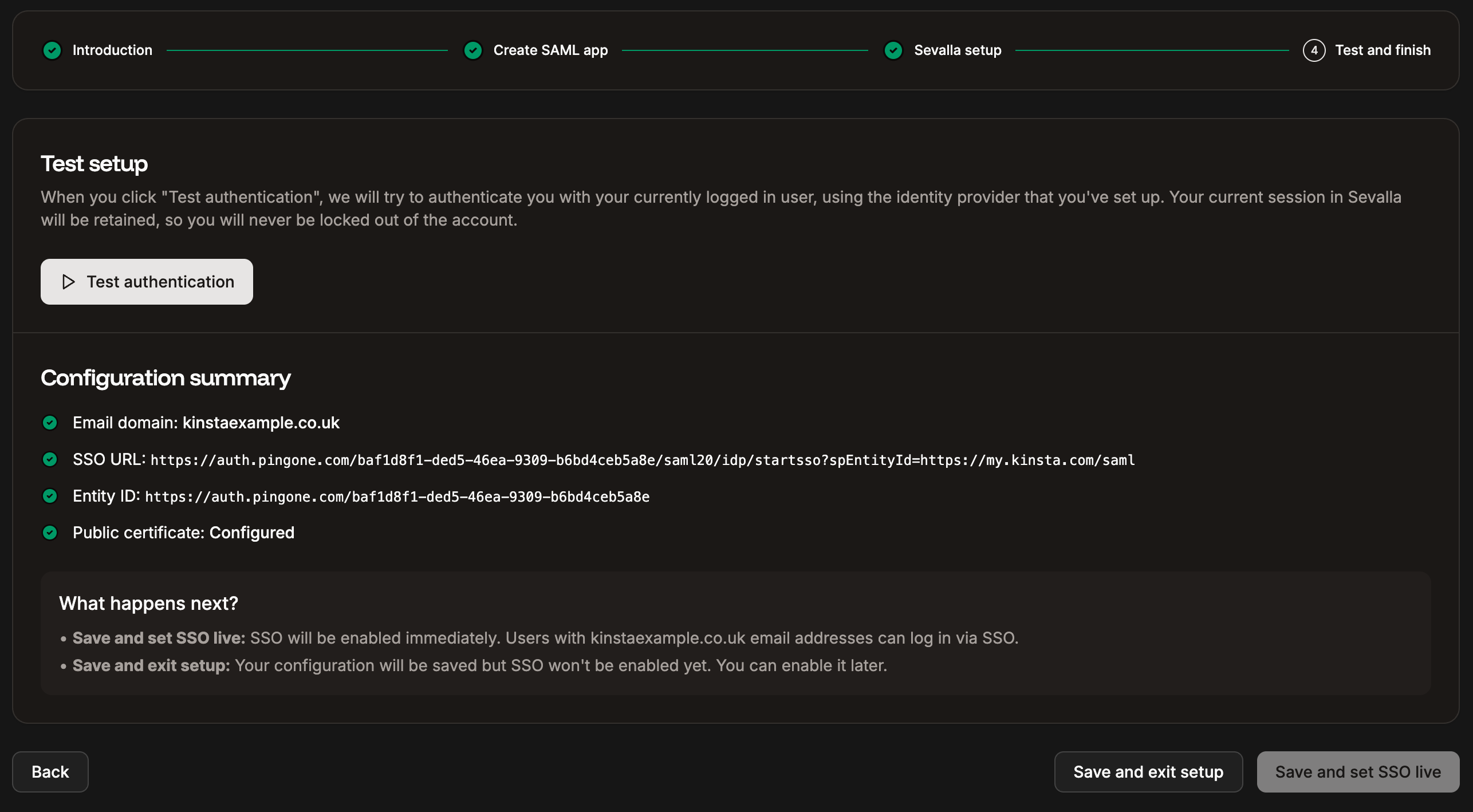
Test the authentication in Sevalla
You cannot enable SAML SSO within Sevalla without first testing the authentication. In Sevalla, within Single sign-on, click Continue until you are on the Test and finish tab, and click Test authentication. A notification appears if the test was successful or if the test fails. If the test fails, click Back and check your SAML settings within your IdP and within Sevalla. If the test is successful and you want to enable SAML, click Save and set SSO live.